I use docker for all of my applications running on my unRAID server, but for nginx I didn't find any image that fulfilled all my needs. So I wrote my own dockerimage which you can find here: https://github.com/Starbix/dockerimages/tree/master/nginx.
The following is my config and should explain what most things do and why.
nginx.conf
This limits the maximal connections per IP
worker_processes auto;
pid /nginx/run/nginx.pid;
daemon off;
pcre_jit on;
events {
worker_connections 2048;
use epoll;
}
http {
limit_conn_zone $binary_remote_addr zone=limit_per_ip:10m;
limit_conn limit_per_ip 128;
limit_req_zone $binary_remote_addr zone=allips:10m rate=150r/s;
limit_req zone=allips burst=150 nodelay;
The custom log format is needed for nginx amplify (statistics and more)
include /nginx/conf/mime.types;
default_type application/octet-stream;
log_format main_ext '$remote_addr - $remote_user [$time_local] "$request" '
'$status $body_bytes_sent "$http_referer" '
'"$http_user_agent" "$http_x_forwarded_for" '
'"$host" sn="$server_name" '
'rt=$request_time '
'ua="$upstream_addr" us="$upstream_status" '
'ut="$upstream_response_time" ul="$upstream_response_length" '
'cs=$upstream_cache_status' ;
access_log /nginx/logs/nginx_access.log main_ext;
error_log /nginx/logs/nginx_error.log warn;
The maximum upload size is 25GB
nginx doesn't send that the webserver is nginx but server
client_max_body_size 25G;
aio threads;
aio_write on;
sendfile on;
keepalive_timeout 15;
keepalive_disable msie6;
keepalive_requests 100;
tcp_nopush on;
tcp_nodelay on;
server_tokens off;
more_set_headers 'Server: secret';
Content will be encoded in brötli (which Safari now supports)
gzip off;
brotli on;
brotli_static on;
brotli_buffers 16 8k;
brotli_comp_level 6;
brotli_types
text/css
text/javascript
text/xml
text/plain
text/x-component
application/javascript
application/x-javascript
application/json
application/xml
application/rss+xml
application/vnd.ms-fontobject
font/truetype
font/opentype
image/svg+xml;
This will include all config files from /sites-enabled. The following configuration is the part you'll configure yourself.
include /sites-enabled/*.conf;
include /nginx/custom_sites/*.conf;
include /nginx/conf.d/stub_status.conf;
}
The preceding configuration is part of the included nginx.conf of my Dockerimage.
/sites-enabled/default.conf
These TLS parameters currently result in a 100% score in all categories on https://www.ssllabs.com/ssltest
upstream php-handler {
server unix:/php/run/php-fpm.sock;
}
ssl_protocols TLSv1.2 TLSv1.3;
ssl_ciphers [TLS13+AESGCM+AES256|TLS13+CHACHA20]:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305;
ssl_ecdh_curve secp521r1:secp384r1;
ssl_prefer_server_ciphers on;
ssl_session_cache shared:SSL:20m;
ssl_session_timeout 15m;
ssl_session_tickets off;
ssl_stapling on;
ssl_dyn_rec_enable on;
resolver 1.1.1.1 1.0.0.1 ipv6=off;
ssl_stapling_verify on;
#RSA certificates
ssl_certificate /certs/example.com/fullchain.pem;
ssl_certificate_key /certs/example.com/key.pem;
#ECDSA certificates
ssl_certificate /certs/example.com_ecc/fullchain.pem;
ssl_certificate_key /certs/example.com_ecc/key.pem;
ssl_trusted_certificate /certs/example.com/fullchain.pem;
I use custom HTTP error pages and I used this for creating them: https://github.com/AndiDittrich/HttpErrorPages
error_page 400 401 402 403 404 500 501 502 503 520 521 533 /error/HTTP$status.html;
This server redirects all of the unencrypted connections to https. It uses the same url, except when it's accessed over the IP address, then it redirects to the root of the domain.
server {
listen 8000 default_server;
server_name _;
include /sites-enabled/headers.conf;
if ($host ~ "\b\d{1,3}\.\d{1,3}\.\d{1,3}\.\d{1,3}\b" ) {
return 301 https://example.com$request_uri;
}
return 301 https://$host$request_uri;
}
This server redirects unused subdomains.
server {
listen 4430 ssl http2;
server_name www.example.com;
return 301 https://example.com$request_uri;
include /nginx/conf.d/hsts.conf;
include /sites-enabled/headers.conf;
}
This is the server that listens on the root of the domain, in my case it redirects to the media subdomain.
server {
listen 4430 ssl http2 default_server;
#listen [::]:4430 ssl http2;
server_name example.com;
include /nginx/conf.d/hsts.conf;
include /sites-enabled/headers.conf;
return 301 https://media.example.com$request_uri;
location /error/ {
alias /www/errorpages/;
internal;
}
}
I use Organizr to organize (duh) all of my apps I regularly use. Definitely check it out if...
]]>
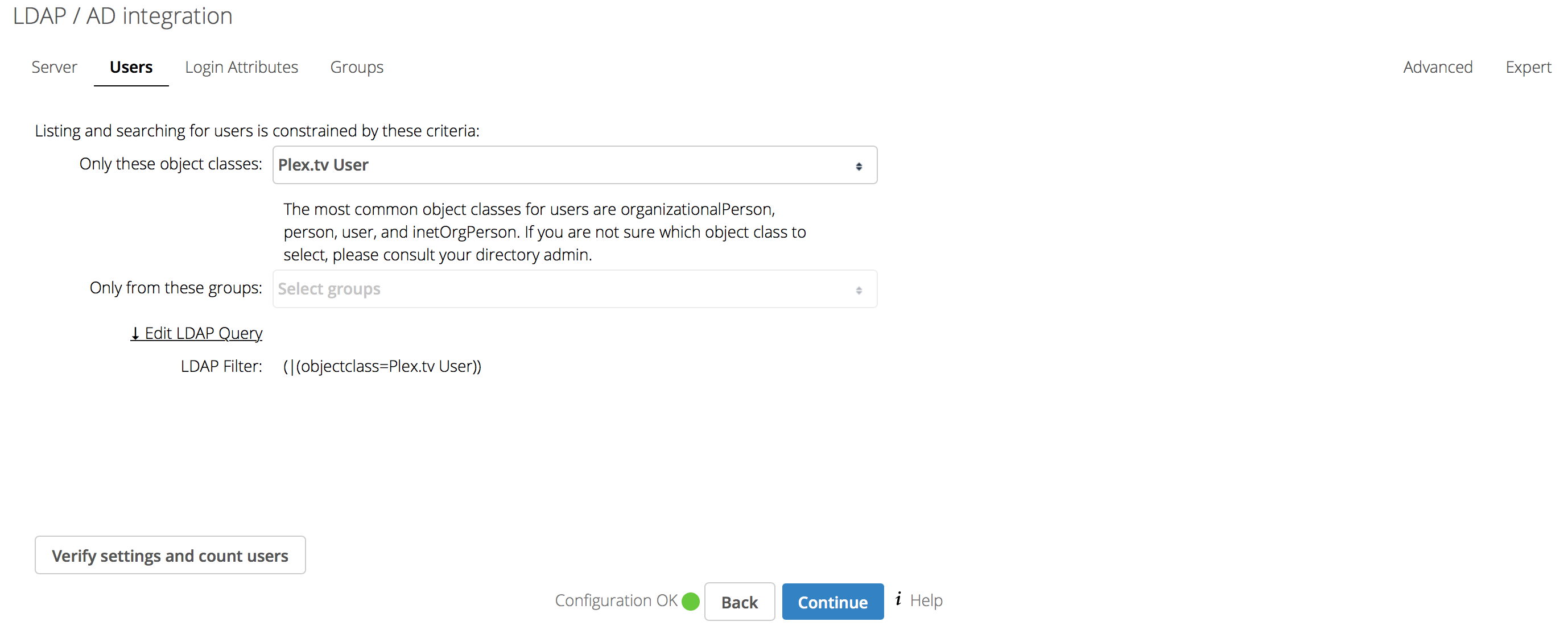
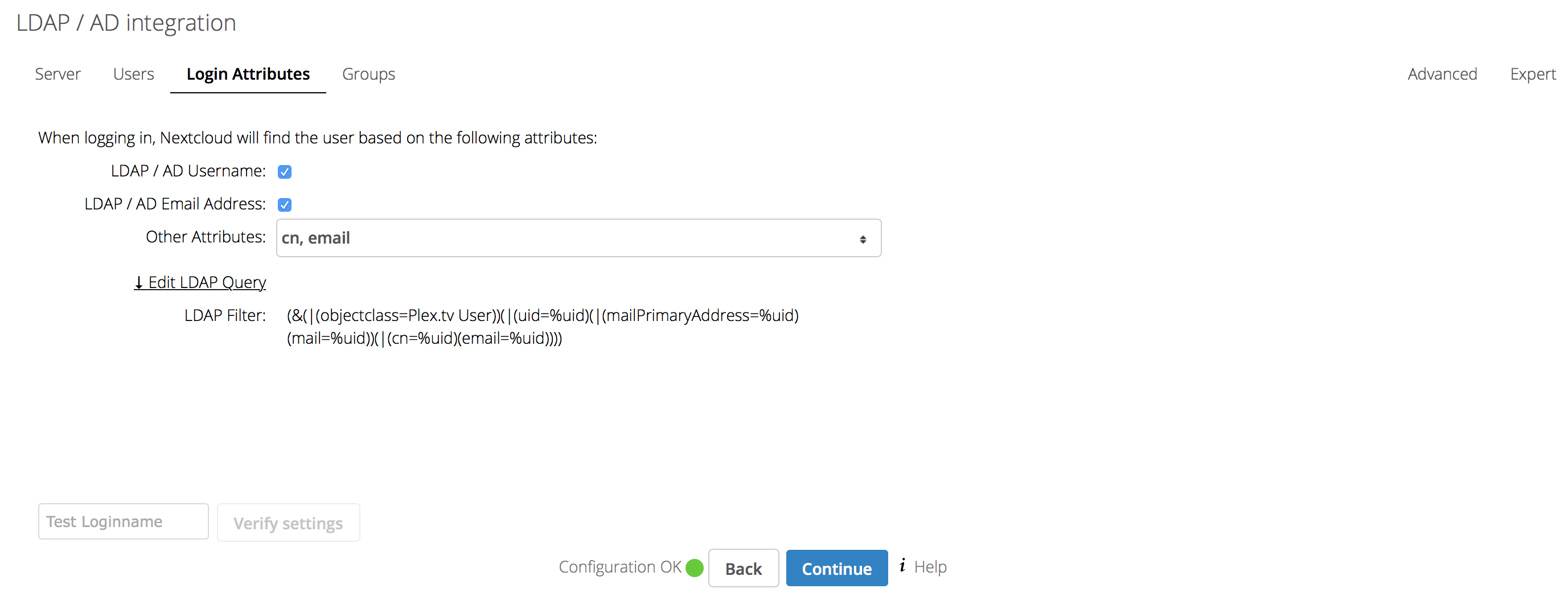
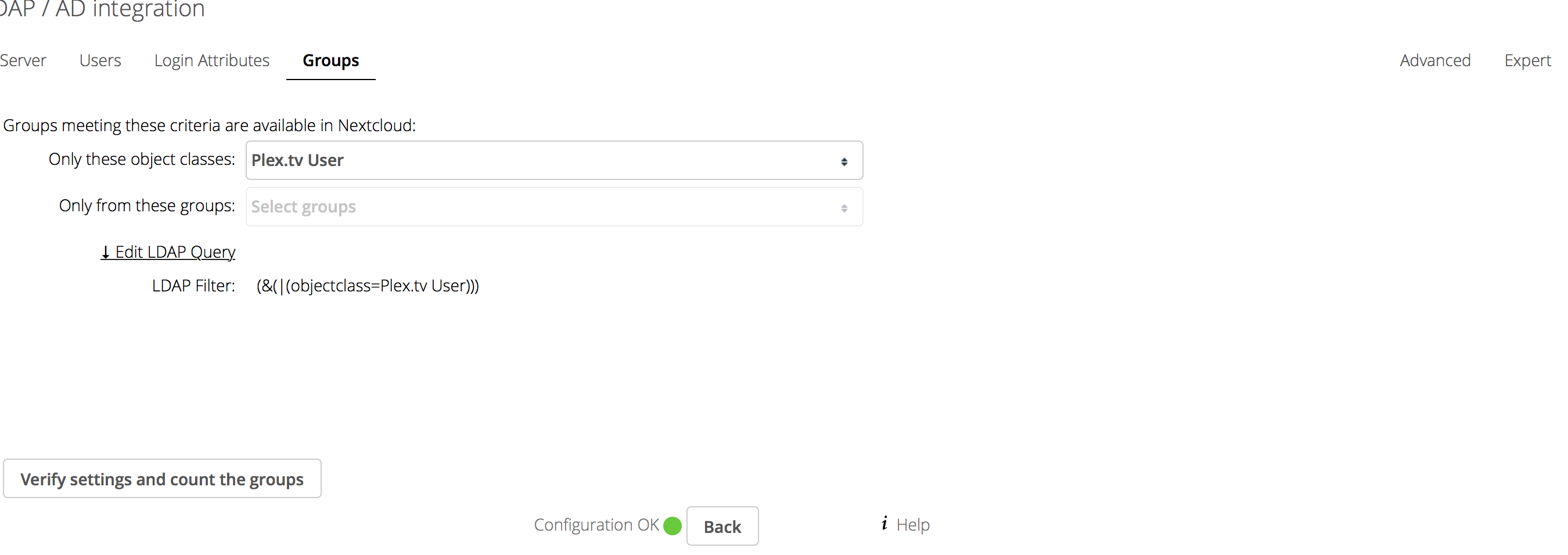
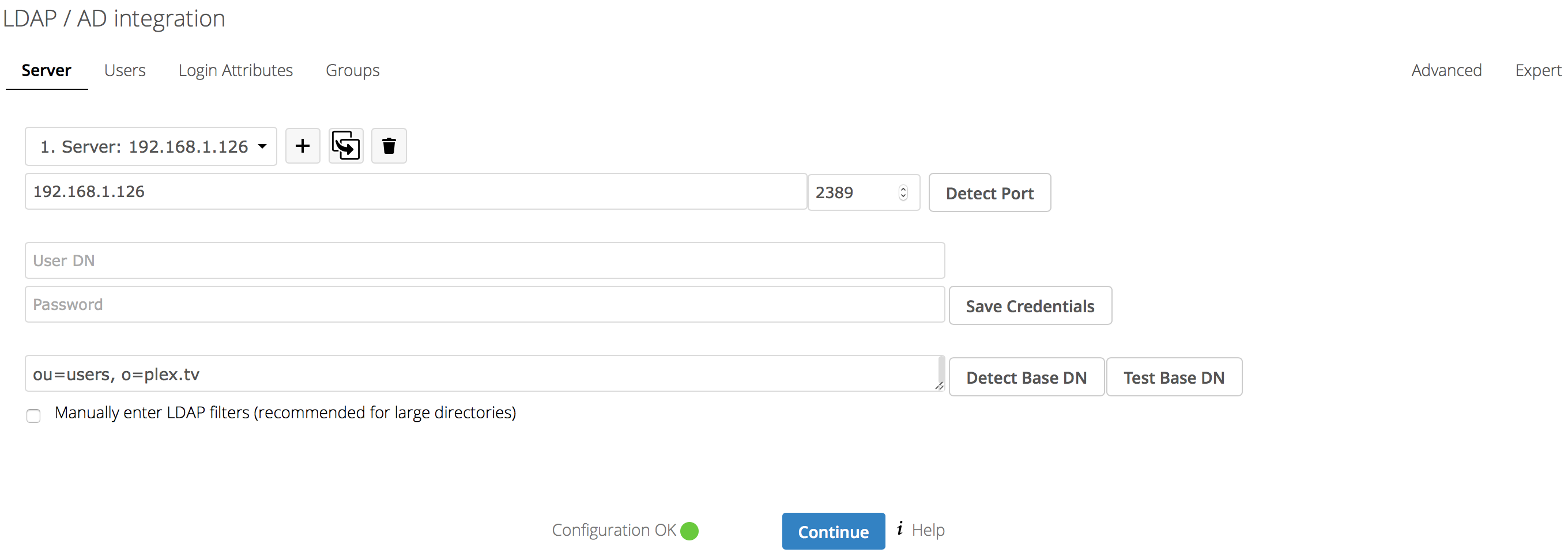 Use the IP your LDAP for Plex instance runs on
Use the IP your LDAP for Plex instance runs on